-
Story
-
Resolution: Done
-
Normal
-
None
-
False
-
None
-
False
-
Testable
-
No
-
-
-
-
-
-
-
1.24.0
-
No
-
No
-
Yes
-
None
-
-
-
RHODS 1.24
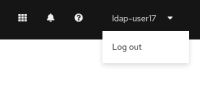
Today we have to start our dashboard with a very permission heavy user to mimic the Service Account that starts it on cluster. Because of this, it is hard to test permissions.
We should put in some impersonation efforts to help get an actual permission layer in for our calls. We'll still need to start with a super user to pretend to be the Service Account, but if we can make all pass-through API calls with a lower permission'ed user, we'd be able to test scenarios better.
- mentioned on